Today’s maritime threats are rarely the reef or weather shore. Instead, maritime operators now face a broad range of concerns from the unknown and difficult to predict specter of terrorism to the routine and burdensome imposition of new and changing local, state, and federal regulations.
ICI Investigations offers innovative and cost conscious solutions. Captain Earl Johnson, 200 ton Master USCG and ICI Investigators can provide in depth investigations, security and Maritime protocols to meet your needs.
- Marine Accident Investigation
- Maritime VIP Protection
- Ship appraisals
- Insurance accident investigations
- VIP vessel security on board and on patrol
- 3D Animation and photography for re-enactment of vessel accidents Worldwide service:
ICI provides Investigations and vessel appraisals.
ICI Investigations Appraised the S.S. United States
http://www.foxnews.com/travel/2018/01/26/once-majestic-cruise-ship-s-s-united-states-could-be-americas-flagship-once-again.html

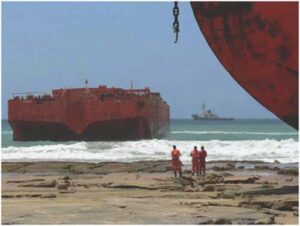
Sinking barges:
ICI’s Maritime Investigation & Expert Witness Testimony Florida — International Consultants & Investigations (ICI) announces today the favorable conclusion of a complex maritime hull claim where ICI was contracted to provide investigative and expert testimony.
As the lead maritime investigator on the claim, Captain Earl R. Johnson explains that while litigation outcomes are always uncertain, the thoroughness of ICI’s maritime investigation and its learned testimony create a measure of confidence in those having to predict litigation outcomes. “It’s what we do,” Captain Johnson explains. “We’re not surveyors and we bring a different set of skills to the table.
We have a lot of experience unfolding complex maritime incidents and that’s where we shine and where we can help lawyers shine too.”
With offices in New York and Florida and with experience working throughout the world ICI is fully capable of providing discrete investigative services and Expert Witness Testimony for Maritime incidents.
1.0 OBJECTIVES:
The purpose of this investigation is to conduct Forensic review and analysis of supplied documents, photos, and statements provided and additional information gathered from subsequent Forensic Research.
Case Related to:
Maritime casualty and subsequent sinking of barges DAR 1 and DAR 2 of the coast of Cape Vidal on October 21, 2008.
The scope of work includes:
1) Forensic review of all photos and documented observations
2) Forensic review and analysis of provided documents with investigators notes.
3) Supporting documents discovered from Internet research
4) Investigators detailed report
Earl R. Johnson, DM, Cll Certified International Investigator 200 ton Masters License, USCG.
PIER A
Analysis of sustainability and useful Economic Life Conducted by International Consultants & Investigations. The following is a preliminary report which examines the sustainability and useful (economic) life of Pier A, the historic iconic landmark located on the waterfront in the vicinity of Battery Park; lower Manhattan, New York City.
A review was undertaken to: (a). understand the historical context of Pier A and its place within the New York City landscape, (b). what has been done to renovate, rebuild and conserve this national historic landmark, (c). interview knowledgeable parties associated with the renovations over the last 10-15 years based upon their knowledge, expertise, and experience in the engineering and architectural concept of the Pier A renovation, and (d). attempt to determine a reasonable “useful use value” of Pier A going forward through the next 50 years.
This report discusses the components of the renovations and improvements which will assist in predicting a reasonable duration of time that the owners, operators, and investors of Pier A might expect this asset to be usable, with normal repairs and maintenance. A realistic useful use economic service life prediction depends on assembling information which is inherently challenging due to the existence of several successive layers of parties including architects, engineers and project managers who have labored over the various renovations that began, stopped , restarted, stopped and finally is near completion as of this writing. If information isn’t available or found in available records, then it became necessary to locate knowledgeable people who participated in the renovation at an earlier time. The report’s reliability depends on the quality of this input. The future sustainability of Pier A largely depends on the dynamic of the tenant developer and Battery Park City Authority’s ability to manage, maintain and be responsive to the public’s enjoyment of the renovated facility. Without question Pier A will reinvigorate the area known as Battery Park. Since 1992, the City of New York recognized that it owned a strategically situated landmark that was in danger of extinction.
At that moment, the existing Pier A, had been allowed to reach the end of its useful life. Pier A dated back to 1884-1886, when it was built by George Sears Greene, Jr., same engineer who had just completed the Brooklyn Bridge. Either the pier had to be replaced, renovated, or sold to a developer. Various alternatives were studied and contemplated. Pier A had been declared a “national historic landmark” in 1976 so incentives and restrictions played a significant role in the available options.
Pier A sits on a special piece of property that lays on the southwest tip of Manhattan, literally the closest landmass to the Statue of Liberty and Ellis Island .The challenges presented by the environment; hostile weather, including but not limited to: salt water, salt air, currents and wind are natural factors that a developer, engineer, and architect must contend. The condition of the pier, above and below the surface needed to be assessed in order to evaluate deterioration and aging. This assessment would assist in determining what improvements would be necessary. Ultimately Pier A’s fate depended on city planners, public opinion and the creativity of developers.
More recently in the 1980’s, Pier A had been a tie up for police patrol boats. Prior to that, Pier A was a fireboat station. For fireboats which stemmed from the days that the FDNY shared the facility with the old Department of Docks. In the early days Pier A served as a place to quarantine arriving immigrants for processing. Pier A was used as a place to welcome visiting dignitaries to the United States. Surviving century old photographs depict a bustling area with Pier A hosting numerous vessels including steam ships, sail boats and ferries. Pier A was always in the midst of New York City nautical history. Pier A’s historical context is the driving impetus, perhaps, to decide over five years ago to utilize the existing iconic structure. This decision provides a seamless historic connection to the City of New York. The oldest surviving pier in New York City would therefore have a future; a useful use for the next 40 years, for the following reasons:
Pier A is being transformed into New York City’s largest restaurant. The unique location of the iconic Pier A and its distinctive iconic clock tower sits at the convergence of the Hudson River, East River, and New York Harbor. The transformation carefully preserved the Victorian architecture with three planned restaurants including an outside plaza for eating and sightseeing, superior space for catering events and an historical information center. This is a destination second to none offered to locals and tourists. The “pier” is adjacent to the Battery Fort, Jewish Holocaust Museum and American Indian Museum which attracts visitors in the shadow of the “new” Freedom Tower. Brand new retail venues including restaurants, schools and residences along an amazing esplanade surround the renovated pier. The embarkation slips for ferries traveling to Staten Island, the Statue of Liberty and the Ellis Island complex provide year round throngs of pedestrian traffic and constantly arriving tourists being dropped off by buses and taxis.
Pier A and Renovation
Pier A was originally built in 1884-1886 as a building which housed the Department Of Docks and New York Harbor Police. There were once over 150 docks and piers in New York City. Pier A is the oldest surviving pier. The original structure is a three level rectangle shaped building extending 300 feet out into the water. It is located at Liberty Place at the southwest tip of Manhattan, just north of the old battery fort with water slips extending the length of both the north and south side of the pier.
The pier deck is now completely renovated with reinforced concrete, pavers, and wooden timbers. All new metal barriers adorn the perimeter of the pier with a surrounding promenade that extends around the whole perimeter of the north, west and south sides of the pier. The building has been completely restored inside and out. Rotted wood has been removed inside and out with new supporting beams replacing rotting wood or supporting old weakened wood.
New fittings and joints have been installed wherever necessary. The whole building is clad in 20,000 square feet of structural steel, galvanized copper, lead metal siding and wood. An earlier siding was installed during a previous partial renovation in 1989.
Pier A engineers have utilized a paint formula which would last and be more impervious to the weather, water and salt environment. The Richter Group formulated a hybrid system of fluoro polymer and flexible acrylic technology that should prove durable in the Pier A environment for 15-20 years. A similar building which used the same paint formula has already demonstrated 13 years of durability and is still going strong.
Improvements below the building on the deck and below the surface of Pier A resulted from assessments and suggestions made by Langan Engineering in 2003 and 2007-8. These suggestions included refilling mortar between stone blocks and restoring several pilings or reinforcing pilings that had been chemically altered by brackish chloride levels through the years. The building utilizes the deck of the concrete and timbers constructed in the late 1800 ’s.
The pier and building on top of it was constructed contemporaneously. Most pier foundations are built to last approximately 50 years. This particular foundation was constructed in a similar fashion to the Brooklyn Bridge just to the East of Pier A. The builders utilized the same machinery, crew and civil engineer. They employed similar technology in constructing the pier foundations.
This report has incorporated information furnished by the engineers who made recommendations and suggestions which were purportedly incorporated into renovation. Renovation and installation of new load bearing pilings and restoration of reinforced concrete at minimum 50 years to the Pier’s service life can be estimated on similar structures cited by engineers that were interviewed for this report.
One engineer who worked on Pier A indicated that typical marine structures are designed for a 50 year useful service life.
The variables depend on the environment where the pier is located and general maintenance. Predictable abnormal weather conditions are a factor that has been built into the pier improvements within the experience of the last 100 years. Structural repairs have been performed at Pier A on the superstructure over time. Presuming the renovations have followed the suggestions set out in the more recent Langan Engineering Report, the serviceable useful life of Pier A below the surface is expected to last until 2065.
Maintenance tests are normally recommended to continually diagnose the condition of the structure including chloride penetration tests and concrete compressive strength tests of mass concrete. Today, Pier A’s concrete no longer suffers from the spoiling. The concrete, cement, and stone have been repaired during renovations over the last 4 years. Observation of some metal structural deterioration due to corrosion of the metal cladding on the deck surface was seen recently. Despite repairs, superstructure elements continue to deteriorate due to the hostile environment. The currents are especially treacherous. Hurricane Sandy apparently did little or no damage below the surface of Pier A.
It is worth repeating that the useful use of Pier A structure will always depend on continuous maintenance and repair.
Pier A Building
Pier A consists approximately 36,900 Square feet, with 35,800 square feet of leasable space. The first floor is being fitted for a huge restaurant featuring an oyster bar with spectacular views of the Hudson River, Statue of Liberty, Ellis Island and the expansive waterfront. The inner walls are covered in some places by ornamental decorative tin type metal cladding of another age. The machines imprinted these impressions no longer exist. Glass throughout the first floor is double pane. Large double pane glass panels line the outside walls and permit inhibited spectacular views. Sliding glass doors are placed to encourage an open air experience during warm days and nights.
Pier A Deck
The Pier A Deck consists of the structure below the building and an outer promenade that surrounds Pier A except for the street approach.
Pier A Approach
The Pier A approach provides vehicular and pedestrian linkage between Battery Place and the Pier A entrance. Under construction presently is a park just to the south of Pier A.
A. South
A water slip abuts Pier A to the south as well as an attached reinforced cement dock which remains from the early part of the 20th century. The WW II American Merchant Mariners Memorial rises out of the water about 40 yards from Pier A and a new promenade which has been built to house an outdoor plaza. This plaza will host outdoor dining and sightseeing. To the south, in close proximity, is the red-bricked circular Battery Fort. West of that landmark, ferries are coming and going with their passengers heading to the Statue of Liberty, Ellis Island and Manhattan day cruises.
C. North
A narrow water slip is situated against the north side of Pier A and its north side promenade. The view north from the Pier A is of a more modern Museum of Jewish Heritage and Holocaust Memorial. Also meandering towards Pier A is The Battery Park Esplanade which approaches Pier A, as another convenient access to Pier A for pedestrians and bikers. One can enjoy spectacular views of the Hudson River waterfront while walking from the new Freedom Tower to Pier A.
Promenade Surrounding the Pier A first floor on the north, west and south is a wide promenade which is similar to a cruise ship walkway. Pedestrians on the promenade are protected by metal and wire railings that feature glass inserts.
These railings are also installed on the inside of the promenade to keep visitors safe from a narrow mote of water below exposing the side of Pier A and the bulwark which was built in the late part of the 19th century. The promenade is new and built to withstand the rigors of New York’s harsher winters for the next 30-40 years. The railings are galvanized to make them impervious to the salt air and poor weather.
Clock Tower
Photographs of Pier A’s clock tower are readily recognizable to visitors, whether locals or tourists. The clock and bell with its’ four faces was a gift of the president of U.S. Steel to New York City in 1919, It was installed as the first memorial to WW I veterans.
Today the clock is and its renovated mechanics remain in the tower awaiting visitors who will learn its history at Pier A’s information center. The old winding staircase that leads to a fourth level clock tower is under renovation and the stanchion where the bell rests is being prepared for many more years of service.
First Floor
The flooring is fitted with durable wood floorboards. A complete renovation of the interior was performed over the last four years including extensive structural repairs including replacement of rotted wood and weakened beams. New steel elements were replaced and off site Dutch repairs to all the windows were performed. Since Hurricane Sandy it was necessary to replace wiring and flooring that was damaged. Security cameras and an expansive sprinkler system have been installed. Weather impervious wiring was installed after the hurricane. All renovations considered preservation of the historical nature of Pier A. Throughout the building is evidence of wooden veneer, plaster cornice work and original molding restoration.
Second Floor The second floor will house an upscale 100 seat restaurant with a newly installed fire place. The second floor will host special events.
Third Floor
A bar is being built on the third floor with offices.
Exterior
The roof has been replaced at least three times during the last 127 years. In the recent renovation a copper tin roof was installed utilizing a more modern gutter system designed to last well over thirty years. A new geothermal HVAC system has been submerged in the Hudson River underneath the pier on the south side. A cage was constructed along with new piles to support the underwater cooling unit.
Preliminary Conclusions
The information gathered for this report has reviewed all components of the present renovations. Each phase of the renovation has been geared to sustainability. The final phase which has been underway over the past year ought to be completed in 90 days. The developers are fitting the new space for three restaurants and a convenient historical information center. The restaurateur has a solid track record of owning and operating over twenty top flight restaurants that have demonstrated a remarkable success story in lower Manhattan. Plans are to install various eateries including a unique oyster bar and upscale 100 seat restaurant and bar. The public will have easy access to the outside promenade where sightseeing will be available as well as food and beverage service. The public will also find the first floor inviting to gain historical information about Pier A and other local attractions.
At the moment restaurants are springing up along The Hudson River Esplanade that follows along the western edge of lower Manhattan. Retail shops and restaurants are being built in and around One World Trade Center a.k.a. the Freedom Tower. This adds up to a unique center of activity drawing visitors like a magnet to the lower end of Manhattan. All information available indicates that the restaurateur is determined to build out a destination that will be a lasting memory for visitors whether they are tourists or locals. The concept has a great potential to contend for the New York City food and entertainment dollar for many years to come.
Pier A has a sustainable useful use for the next 35-40 years. Sustainability depends on continuous maintenance, a visitor’s sense of security and adjustments to market trends by the restaurant owner. The engineers and architects selected by the Battery Park City Authority have handed over Pier A to the restaurant developer and Dermot Company to steward this unique property through the next 35- 40 years.